Solutions

Splunk Security Solutions
From SIEM to SOAR, Splunk equips security teams with the tools they need

What is Splunk Security?
In today's digital landscape, safeguarding your organisation's data and infrastructure is more critical than ever. Splunk offers cutting-edge security solutions that leverage advanced analytics and machine learning to provide comprehensive security monitoring, rapid incident response, and actionable threat intelligence. From SIEM to SOAR, Splunk equips security teams with the tools they need to detect, respond to, and mitigate security threats effectively.
Talk to an Expert
Get in touch with Somerford Associates to discuss your Splunk Security needs and explore the services we offer.
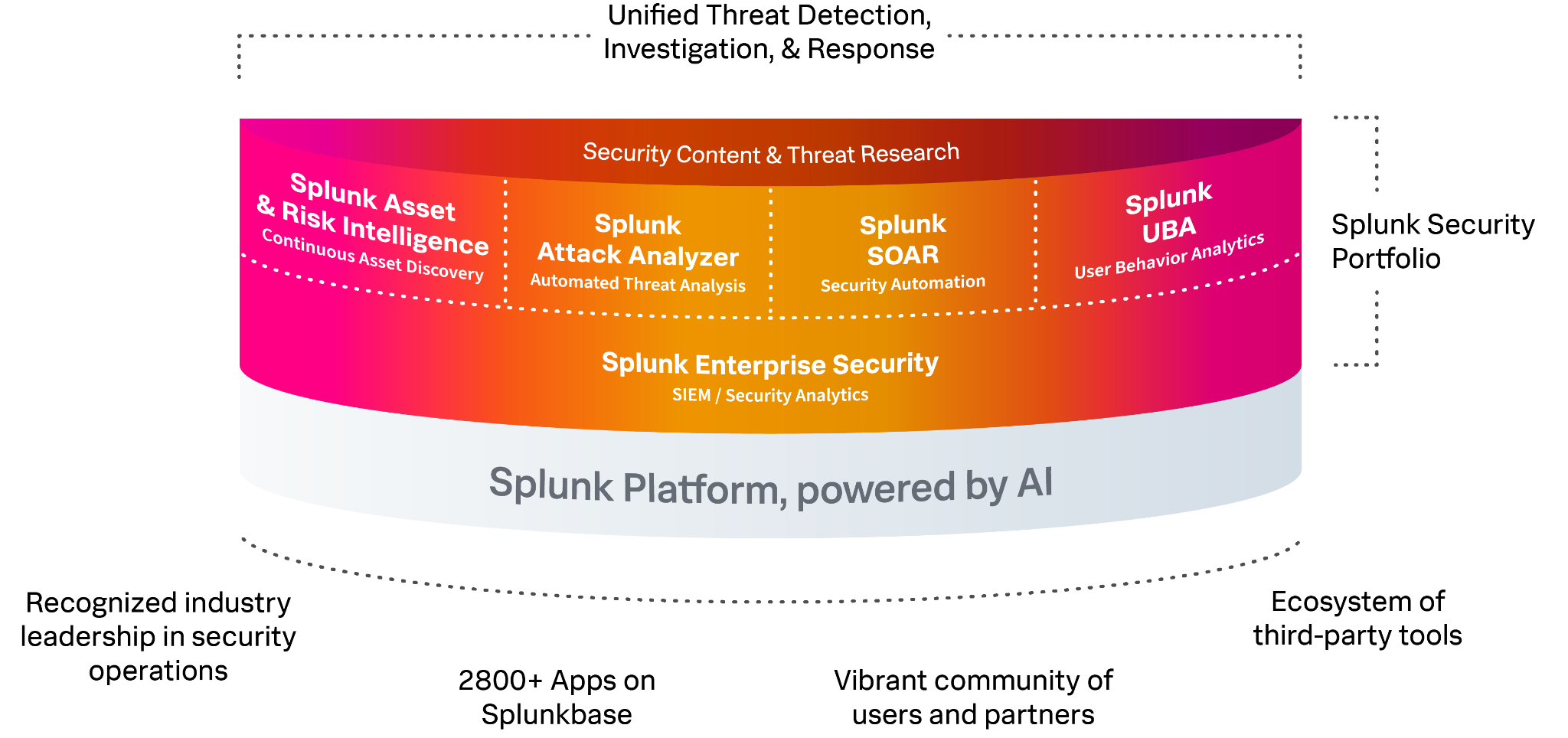
The Splunk Security Suite
Splunk's suite of security solutions is designed to provide a unified and robust defence against cyber threats. Here’s a closer look at what Splunk offers:
Splunk Enterprise Security (ES)
A SIEM solution that delivers real-time monitoring, advanced threat detection, and risk-based alerting. It helps organisations gain visibility into their security posture and ensures compliance with industry regulations.
Splunk Phantom
A SOAR platform that automates and orchestrates security operations. It enables faster incident response through automated workflows, case management, and seamless integration with other security tools.
Splunk User Behavior Analytics (UBA)
This tool uses machine learning to detect anomalies and insider threats. By analysing user and entity behaviour, it identifies unusual activities that may indicate security risks.
Splunk Mission Control
A unified security operations platform that integrates Splunk ES, UBA, and Phantom. It provides centralised management and real-time threat intelligence to enhance situational awareness and collaboration.
Splunk Intelligence Management
Formerly known as TruSTAR, this solution enhances threat intelligence by aggregating data from various sources. It automates the enrichment of security events and integrates with existing security workflows for operational efficiency.
Splunk Security Essentials
A resource hub providing pre-built detections, dashboards, and best practices. It helps organisations maximise their use of Splunk's security solutions with community-driven content and ongoing updates.
Get in touch for a demo of Splunk Security solutions
Enhance your Security capabilities with Splunk, ensuring your digital systems are reliable, efficient, and scalable.
What Benefits Does Somerford's End-to-End Splunk Professional Services Offer?
Expert Knowledge & Guidance
Receive expert insights on Splunk, gaining a comprehensive understanding of optimal practices and tailored recommendations to maximise the returns on your investment.
Accelerate Implementation
Harness the expertise of Splunk professionals to achieve greater outcomes in a shorter timeframe.
Faster ROI
Employing our Professional Services offers the quickest and most efficient approach to deploying your Splunk solution, ensuring rapid time-to-value.
"Somerford has helped guide us through our Splunk journey, they’re always happy to help and have been eager to get the best value possible out of our Splunk license."
Dylan E.Senior Security Analyst
Resources
Assisting a major UK retailer group in addressing security and risk management issues with a Future Security Operating Centre (SOC)
| Case Study
Upcoming Splunk Events
- 18th April 2023
- 10:00 am
A Journey Through Security Maturity—Splunk Webinar Series
- Splunk, UAE, UK, Webinar
- 27th November 2024
- 11:51 am
Resilience Talks LinkedIn Live: Splunk State of Observability 2024
- Splunk
- 29th November 2024
- 3:56 pm
Being Data Observant: Embracing Observability and AI Resilience with Splunk | S05 – E07 | Somerford Podcast
- Splunk
- 18th February 2025
- 4:07 pm
Navigating Through the DORA Effect | S06 – E01 | Somerford Podcast
- Splunk
- 27th February 2025
- 12:16 pm
Exploring Operational Resilience with Shaun Cooney at Splunk | S05 – E02 | Somerford Podcast
- Splunk
- 27th February 2025
- 12:27 pm
Helping Specsavers see data clearly with Splunk ITSI & Observability | S04 – E02 | Somerford Podcast
- Case Study, Splunk
Get in Touch to Learn More
Contact us to be in touch with our certified and expert team. Find out how Somerford can transform your digital operations.






