Elevate Security and Access Management with Okta

What is Okta?
Discover the power of seamless identity and access management with an official Okta partner. In a digital world where security is paramount, our partnership equips you with advanced solutions that streamline access while fortifying your organisation's defences.
Leverage Okta's industry-leading platform to manage identities, enforce access policies, and safeguard sensitive data. Okta ensures you have the tools to confidently navigate today's evolving security landscape.



Partnership
As a trusted Okta partner, we proudly hold an Activate status, signifying our deep expertise in Okta's solutions. This partnership underscores our commitment to providing you with exceptional guidance and tailored solutions.
Somerford Professional Services
Somerford Associates is a certified Activate Partner with Okta and an Okta user since 2016. Our team includes security-cleared Consultants, Engineers, an Okta Technical Champion and Project Managers, who have implemented Okta in some of the largest and most complex organisations and Government Departments.
-
Partnership for
7 years -
Okta Certified
Professional Consultants > -
SC & DV Cleared
Professionals - Okta Activate Partner
Strengthening Your Security Infrastructure with Okta's Robust Solutions
Single Sign-On (SSO) Implementation
Multi-Factor Authentication (MFA) Integration
Identity Lifecycle Management
Access Policy Enforcement
Secure API Access Management
Ready to Fortify your Security and Streamline Access Management?
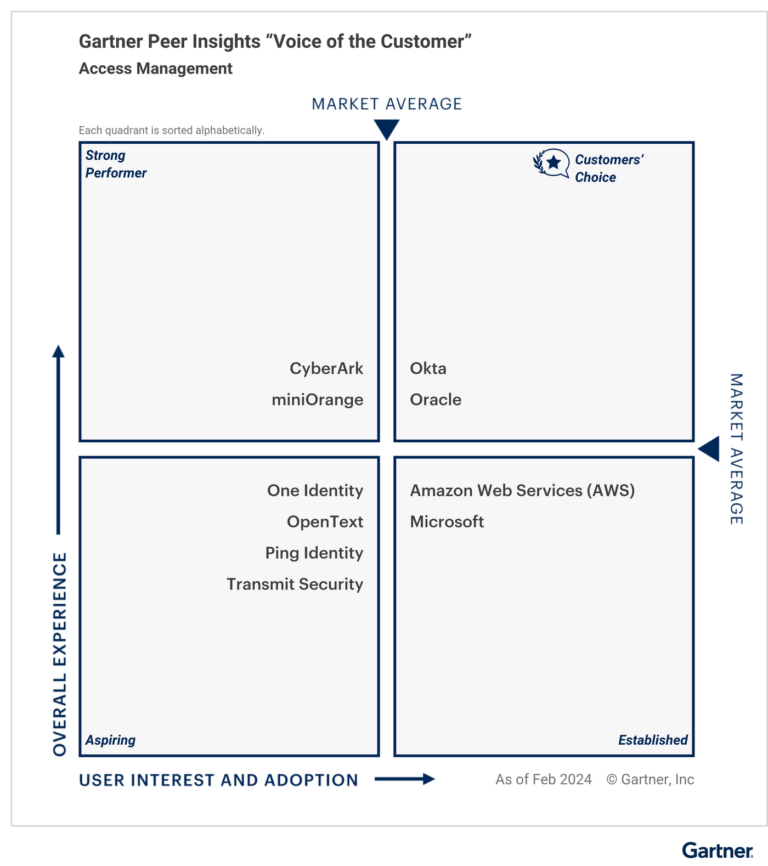
Okta Recognized as a 2024 Gartner® Peer Insights™ Customers' Choice in Access Management
How to Implement Strong Authentication — Introduction & Demo
Understand Okta Identity Management in just 60 Seconds

Dedicated Support Desk
Our partnership with Okta brings you cutting-edge identity and access management solutions. Okta's advanced technologies secure user identities, streamline access and fortify your organisation against modern security challenges. With our joint expertise, we empower businesses to navigate the digital landscape with confidence.
