Warning: Undefined array key "providerNameSlug" in /home/somerfordassocia/public_html/wp-content/plugins/wpseo-video/classes/class-wpseo-video-embed.php on line 136

Identity is the New Perimeter: Moving Beyond the Vault
Author: Matt Ord
Release Date: 21/04/2026
The Erosion of the Firewall
The first lesson in cybersecurity, still to this day, follows that of ancient civilisations: build a bigger wall. Firewalls are the “moat and castle” defence of the digital age, but what happens when your network can no longer be contained? In a world of remote work and cloud-first operations, there is no longer a physical inside to protect.
To be absolutely clear: firewalls aren't dead. If you are connecting to a datacentre or protecting core servers, you are still traversing a firewall, and they remain a necessary layer of infrastructure defence. However, the paradigm has shifted. Users are becoming far less protected by these traditional perimeters because they now operate outside them. The firewall simply isn't the primary shield for user protection anymore.
Think of it this way: If you were tasked with defending Jamaica, you could build a wall. But if you’re defending Indonesia, a nation of 17,000 islands, a wall is impractical. This is the reality of modern businesses. To stay secure, we must stop trying to guard the network and start focusing on the individuals within. This shift to identity-centric security recognises a new truth: in the modern enterprise, identity is the new perimeter.
Why Legacy Vaulting Can't Keep Up
For years, the digital vault was the gold standard; a secure "black box" where we locked away our most sensitive credentials. However, in a high-speed cloud environment, legacy vaulting has mostly shifted from a security asset to a major liability.
Now, to be fair to traditional methods, we will always need a secure place to store certain things. There will always be some highly sensitive, static credentials like break-glass accounts or root keys that need to be stored and managed by a robust Privileged Access Management (PAM) solution.
The core issue, however, is "Always-On" risk. Traditional vaults often grant permanent, standing privileges. If a high-level user is compromised, the keys to your entire kingdom are exposed 24/7. In our hypothetical of 17,000 islands, relying on static vaulting is like leaving a master key under the doormat of every single home. Furthermore, manual password rotation simply cannot keep pace with the reality of modern infrastructure.
Today, we rely heavily on ephemeral credentials: short-lived access tokens that might exist for just five minutes. This is particularly crucial for cloud workloads, automation pipelines, and ticketing systems where access can, and must, be automated. Modern PAM is no longer just about where you store a password; it’s about managing the dynamic relationship between the user and the resource in real-time.
Achieving Zero Standing Privileges (ZSP)
To secure a modern network, we have to change our fundamental goal. That goal is Zero Standing Privileges (ZSP). This is the concept that no user, regardless of their rank, should have administrative rights by default.
For standard users, there will always be a baseline level of defined, day-to-day access. Admin users, however, shouldn't have perpetual keys to the kingdom sitting on a shelf waiting to be compromised. Instead, admins must constantly prove the Five W’s.
The five W's of access control; Who, What, When, Where, and Why form a foundational framework for managing security permissions, ensuring only authorised users have the necessary access to resources.
"The zero standing privilege model prevents users from maintaining access they don’t need and reduces the passwords, secrets, and keys a company must maintain to remain secure." - StrongDM
With ZSP, the account holds no power until it is strictly needed. This changes the game for attackers: if a hacker compromises an account with zero standing privileges, there is no “access” for them to "harvest."
Modern PAM & Just-in-Time (JIT) Access
How do we achieve ZSP without slowing down the business? The answer is Just-in-Time (JIT) privileged access. Think of JIT as a digital boarding pass that only works for one specific flight at one specific time. Access is granted on-demand, for a specific task, and for a strictly limited duration.
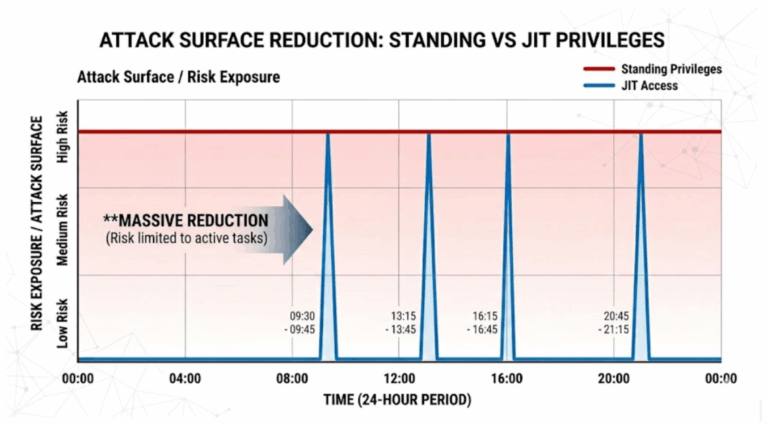
This model relies heavily on ephemeral credentials for cloud environments. These are short-lived tokens that expire automatically the moment the task is complete. By using JIT, you eliminate the risk of "orphaned" accounts or leaked long-term passwords. It reduces your attack surface to the smallest possible window of time, ensuring that even if a credential is intercepted, it is useless by the time an attacker tries to use it.
Building a Zero Trust Identity Architecture
JIT and ZSP are the building blocks of a broader Zero Trust Identity architecture.
Drawing heavily on the UK’s National Cyber Security Centre (NCSC) design principles for Zero Trust, we must define this clearly: Zero Trust means moving away from inherent trust based on network location. It requires a single, strong source of identity. It dictates that we must authenticate and authorise every single request, evaluating the context of the user, the health of the device, and the specifics of the service being accessed, before granting entry. In this framework, “trust” is never assumed based on location or past behaviour; it must be continuously verified at every step.
Delinea provides the identity-first platform necessary to see, manage, and audit every privileged interaction across your entire “archipelago.” By using automation to grant and revoke access, your DevOps and IT teams can move at cloud speed without sacrificing security. You get total visibility into who is doing what, where, and why, without the bottleneck of manual vault management.
Conclusion: Secure Your Future with Delinea
The traditional network perimeter has dissolved. Historically, a robust firewall and a secure digital vault were sufficient to keep threats at bay, but the landscape has irrevocably changed. Organisations can no longer rely solely on the static walls of yesterday to protect the distributed, dynamic "islands" of today's enterprise.
The reality is stark: relying on the "moat and castle" logic of legacy vaulting and leaving standing privileges unchecked across cloud environments leaves critical infrastructure exposed. Managing risk today requires accepting a fundamental shift: identity is no longer merely a subset of a security strategy; identity is the security.
It is time to evolve. Embracing Zero Standing Privileges (ZSP) and Just-in-Time (JIT) access is not just an exercise in ticking compliance boxes; it is about enabling the business to operate securely at cloud speed, without the friction of outdated security models. With Delinea, organisations can make that transition smoothly, shifting from a posture of implicit, always-on trust to continuous, identity-driven verification.

